You must provide a substantive response to the main discussion question and following your initial post reply to two (2) other fellow student’s postings. Your reply should be positive. A substantive response to the main question should be a minimum of 200 words, not including references. Replies should be thoughtful. Do not consider a reply such as “Great post” substantive.
Need a minimum of 3 APA style references for each reply
Asecurity incident is any attempted of unauthorized access, use, disclosure, modification, or destruction of information. This includes interference with information technology operation and violation of the policy, laws or regulations. Examples of security incidents include are Computer system breach, Unauthorized access to, or use of, systems, software, or data, Unauthorized changes to systems, software, or data, Loss or theft of equipment storing data, Denial of service attack, Interference with the intended use of IT resources and Compromised user accounts.
It is important that actual or suspected security incidents are reported as early as possible so that company can limit the damage and cost of recovery which includes specific details regarding the system breach, vulnerability, or compromise of your computer and we will respond with a plan for further containment and mitigation.
No investigation can be successful if the computing infrastructure will not support the basic requirements of good information security. The FBI has estimated that fewer than ten percent of all computer incidents get reported, fewer than ten percent of those get investigated, fewer than ten percent of those result in prosecution, and fewer than ten percent of the prosecutions result in conviction and punishment which means the computer criminal has a one in ten thousand chance of going to jail for a computer-related crime for any endeavor. Solid investigation can change those odds materially.
Implement appropriate policies, standards, and practices. Ensure that legal Problems (such as privacy and ownership of company information) are documented in appropriate policies.
Implement, equip, and thoroughly train a computer incident response team (CIRT).
Implement appropriate access controls.
Implement appropriate vulnerability testing.
Implement real time intrusion detection and logging.
Institute periodic incident response rehearsals and drills.
Institute and maintain relationships with local law enforcement agencies.
References:
Sec. (n.d.). Report a Security Incident | Information Security Office. Retrieved from https://security.berkeley.edu/quick-links/report-security-incident
Stephenson, P. (n.d.). Investigating a computer security Incident. Retrieved from http://www.ittoday.info/AIMS/DSM/82-02-65
Windows Registry
The critical aspect of the windows operating system is the windows registry, which maintains the configuration aspects of the system. The historical information of the user is also maintained by the windows registry (Carvey, 2016). The details in the windows registry are similar to that of the log files. Some of the activities that the windows registry maintains are the information about the user profiles and user activities, keeping a log of the installed applications, a log of the opened apps, active apps, etc. Some of the handy information that serves a digital forensic analyst while studying the windows registry is
Record of the applications opened by the user.
Record of the access control by the user.
Record of the wired and wireless connections established by the user.
Record of the activities performed by the user.
The above information can clearly define the activities of a convict in a forensics case and helps law enforcement to gather the evidence that proves the guilty.
Registry Analysis
It is the analysis that is carried out after extracting the image of the system. This is one of the first steps of analyzing the windows registry. This gives a scope for the investigator to dig into the hive files of the windows registry. Registry keys are used to look into the contents of the windows registry (Carvey, 2016). The spectrum of activities that are carried out in a windows registry analysis is
Extracting the special keys that enable to have access to the hive files.
Retrieval of data from the hive files.
The scope of analysis can be extended with the above two steps.
Correlating the data collected from the hives to the existing case.
Registry keys help the analysts understand the registered activity from the apps. The file access times are registered, and they are extracted from the registry key values.
References
Carvey, H. A. (2016). Windows registry forensics: Advanced digital forensic analysis of the Windows registry. Amsterdam: Syngress.
Essay Writing Service Features
Our Experience
No matter how complex your assignment is, we can find the right professional for your specific task. Achiever Papers is an essay writing company that hires only the smartest minds to help you with your projects. Our expertise allows us to provide students with high-quality academic writing, editing & proofreading services.
Free Features
Free revision policy
$10Free bibliography & reference
$8Free title page
$8Free formatting
$8How Our Dissertation Writing Service Works
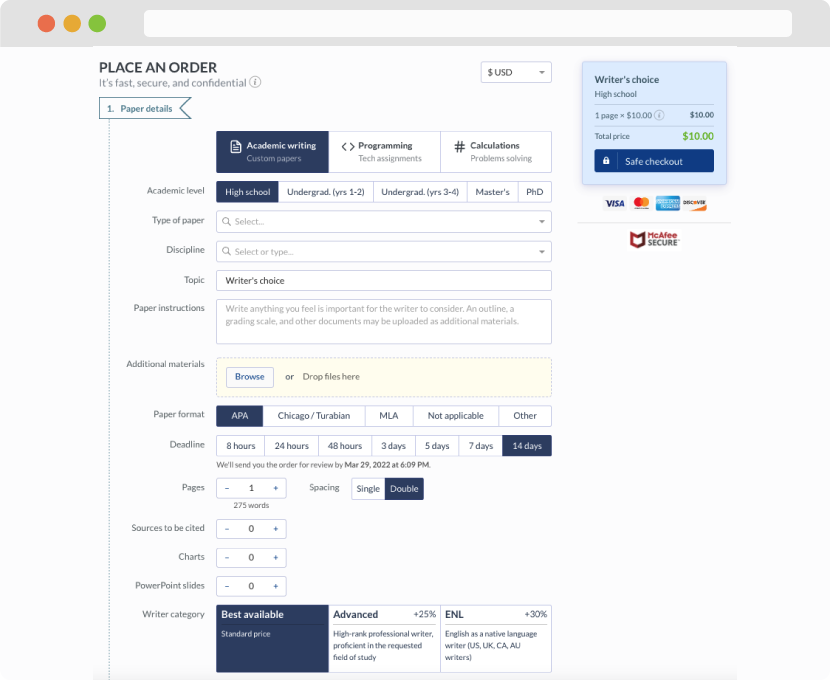
First, you will need to complete an order form. It's not difficult but, if anything is unclear, you may always chat with us so that we can guide you through it. On the order form, you will need to include some basic information concerning your order: subject, topic, number of pages, etc. We also encourage our clients to upload any relevant information or sources that will help.
Complete the order form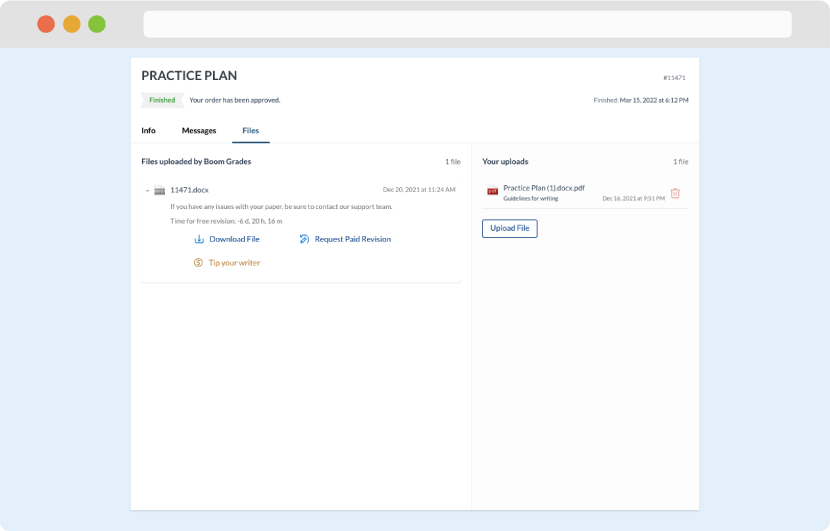
Once we have all the information and instructions that we need, we select the most suitable writer for your assignment. While everything seems to be clear, the writer, who has complete knowledge of the subject, may need clarification from you. It is at that point that you would receive a call or email from us.
Writer’s assignment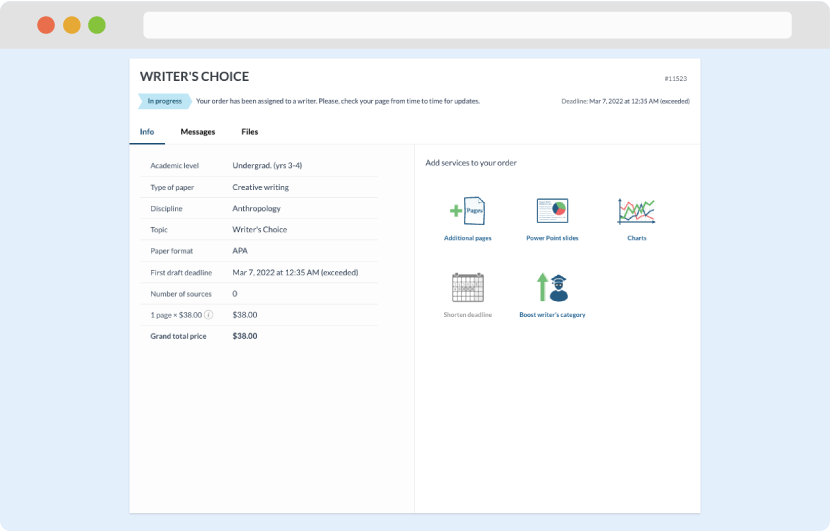
As soon as the writer has finished, it will be delivered both to the website and to your email address so that you will not miss it. If your deadline is close at hand, we will place a call to you to make sure that you receive the paper on time.
Completing the order and download