Class Discussions
Response to each of the following 4 problems:
Problem 1: CLABSI: Central Line- associated Bloodstream Infection. Increased number of infections is an issue that has recently became an issue in my hospital.
Central and PICC lines are required to be assessed and flushed at least once a shift however this may change depending on the patient’s cognitive status. Curo’s caps much be changed every four hours and dressing changes should be every seven days. Currently, we have been having a fall-out on keeping the dressings intact and how to properly change the dressing using sterile technique. I think teaching would be beneficial so that each nurse can have a clear idea on how to do certain skills depending on their intent. Even seasoned nurses sometimes need a helpful refresher in order to remind them of the guidelines in place and possibly learn any new evidence-based practice regarding this concept. I think one obstacle for the learner when in a group setting would be the lack of one-on-one attention in order for the learner to feel comfortable with this skill especially new nurses. Typically, in a group setting, learns typically watch the educator preform the skill and then the learners try themselves at the same time with only one educator present. This could discourage the learner from asking any questions or the educator could miss a teaching point for the learner. One possible barrier would be how to think of a way for nurses to maintain this information or have it somewhere it can easily be accessible.
Problem 2: Fall prevention: Nurses are not using the necessary equipment or using safety tools in order to prevent a patient from falling and possibly causing injury.
The expectation when it comes to fall prevention is that bed and chair alarms are on and audible along with both items being plugged into so that way an alarm may come through the nurses phone. If the patient has an unsteady gait or the nurse is unsure about the gait, they must use a walker and a gait belt around the patient. If the patient must be removed from bed there is other equipment available such as the hoisting machine. Currently, bed or chair alarms have not been plugged in and nurses are leaving patients on the toilet alone where they could possibly pass-out or get up without telling the nurse and falling. A teaching lesson may be beneficial to help this issue as there is several amounts of equipment to help move the patient if they are unable to ambulate with a gait belt or walker. A lesson about the equipment would also be helpful to help a patient get back into bed if the patient is too heavy from picking them off the floor. I feel like this activity would also be more effective in a one-on-one lesson since usually in a group there is less opportunity for everything to have a chance to practice on new equipment. One barrier would be assuring a way that all alarms are turned on throughout the shift as patients are constantly moving around their rooms.
Problem 3: Nurse Burnout:
Nursing burnout has always been present prior to the pandemic but has just recently been in the spotlight as we are on the frontlines. The emergency room is a physically, mentally, and emotionally stressful environment. Burnout amongst nurses leads to an interest in patient’s safety events and a decrease in patient satisfaction. The exhaustion at work carries over into the nurse’s home life which causes unhappiness in the home. Education to new graduate nurses regarding ways to prevent burnout by staying physically, mentally, and emotionally healthy would implement this value early in their career. An obstacle for the learner (new graduate nurses) would be having to participate in a work-related activity while at home due to group restrictions during COVID. Also, they might be naive to the topic of burnout and not take the education seriously. A barrier to educating this group would be finding ways to engage with them in these preventative measures.
Problem 4: Opiod education:
There has been a rise in emergency room visits for opioid related causes over the past decade leading the current opioid epidemic (Virginia Commonwealth University, 2020). A recent article showed there was an increase of 123 percent in non-fatal opioid overdoses over the past year in the Richmond area. Education needs to be provided to the community regarding these numbers and ways to prevent these events. Obstacles would include community participation and means to reaching out to the community.
Essay Writing Service Features
Our Experience
No matter how complex your assignment is, we can find the right professional for your specific task. Achiever Papers is an essay writing company that hires only the smartest minds to help you with your projects. Our expertise allows us to provide students with high-quality academic writing, editing & proofreading services.
Free Features
Free revision policy
$10Free bibliography & reference
$8Free title page
$8Free formatting
$8How Our Dissertation Writing Service Works
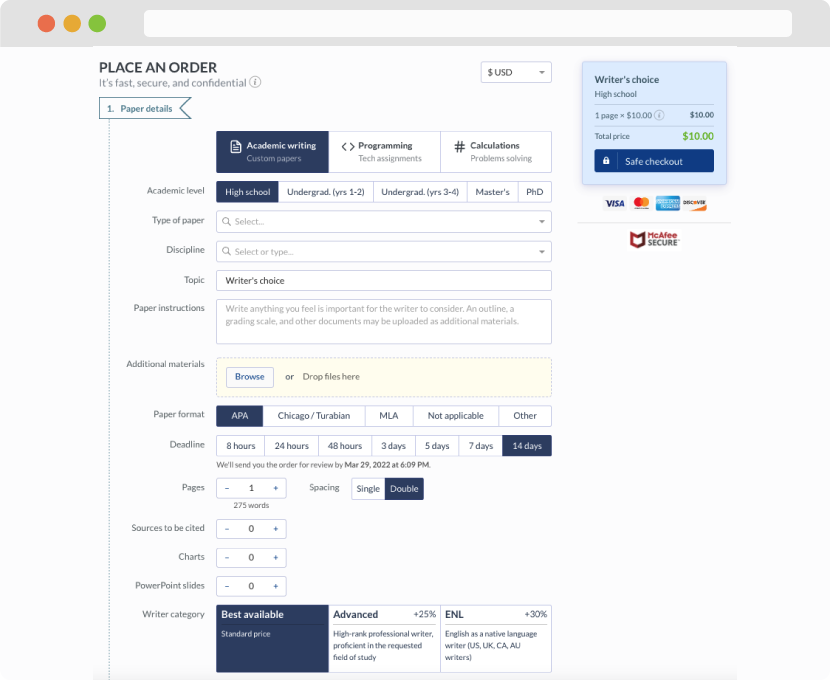
First, you will need to complete an order form. It's not difficult but, if anything is unclear, you may always chat with us so that we can guide you through it. On the order form, you will need to include some basic information concerning your order: subject, topic, number of pages, etc. We also encourage our clients to upload any relevant information or sources that will help.
Complete the order form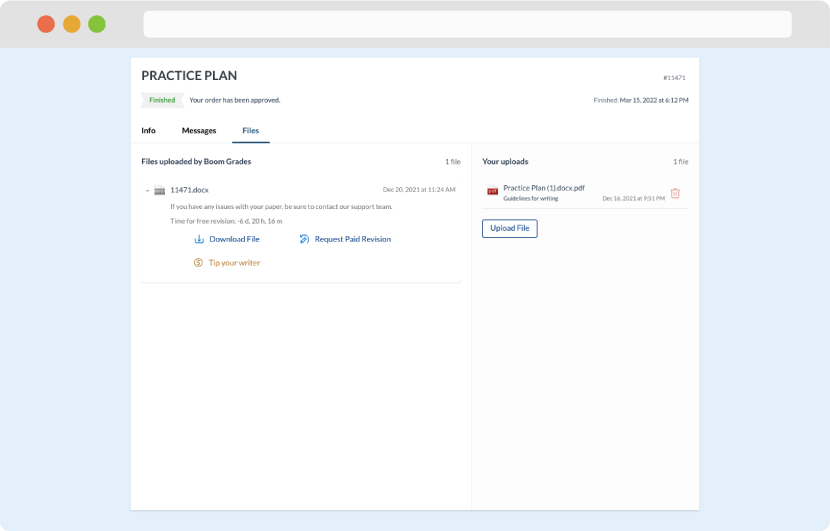
Once we have all the information and instructions that we need, we select the most suitable writer for your assignment. While everything seems to be clear, the writer, who has complete knowledge of the subject, may need clarification from you. It is at that point that you would receive a call or email from us.
Writer’s assignment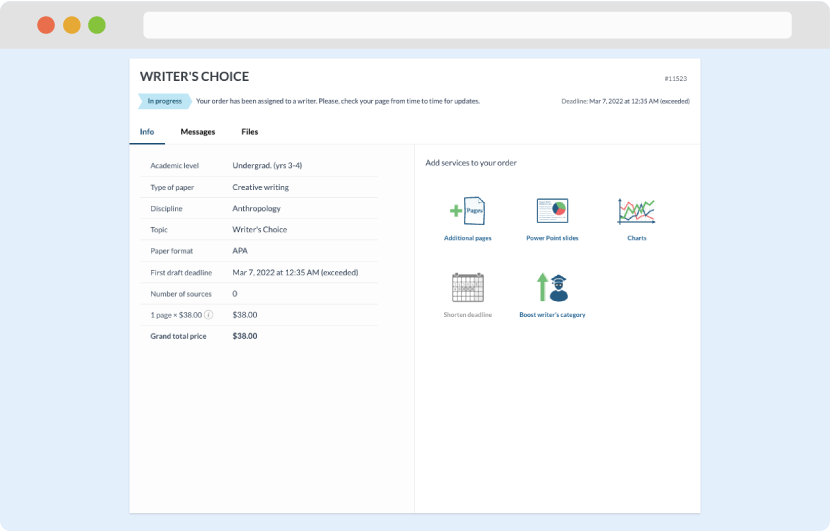
As soon as the writer has finished, it will be delivered both to the website and to your email address so that you will not miss it. If your deadline is close at hand, we will place a call to you to make sure that you receive the paper on time.
Completing the order and download